Small applications
Bunch of application not deserving direct link from the main page.
Picture to hex/bin converter
Alpha build. Features:- files conversion between few formats including raw (resolution is limited),
- picture export (pixels color values, not file bytes) to file: monochrome 1 byte per pixel or B/W 1 bit per pixel - threshold is 128/255
PICtoC.zip (442kB)
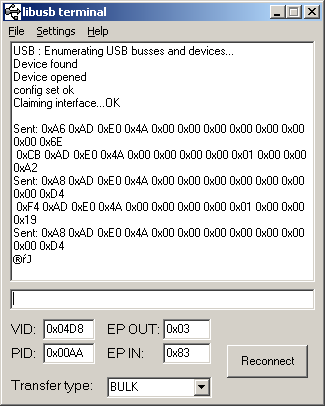
Pseudo-terminal libusb
RS232-like terminal for devices using libusb-win32 driver. Recommended use with libusb-win32-device-bin-20051120.2006.08.31 Added data display as hex string.
libusb_terminal_bin_20060418.zip (323kB)
libusb_terminal_bin_20060831.zip (334kB)
Source (BCB6 PE), GPL v2
Binary files to C-like table converter
Input files can be treated as byte, word or int type (little endian). There are many similar tools, but I didn't found one with word conversion that I needed. Features: user-defined separator between hex values (default comma + space) and line wrap length (default over 70 chars)bin2hex.c
windows executable: bin2hex.exe (26kB)
linux executable: bin2hex (12kB)
Hexadecimal to file converter
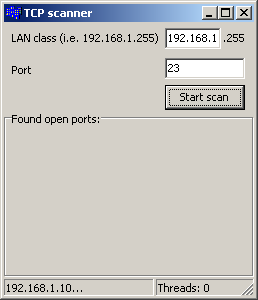
hex2bin.zipTCP scanner
First look at Turbo C++, small application to search LAN for machines with open selected port. Gotcha's: static linking (Linker/Linking/Use dynamic RTL + Packages/Build with runtime packages), Synchronize(&UpdateCaption);, TThread's OnTerminate different than in BCB4-6.skaner_tcp.zip (366kB)
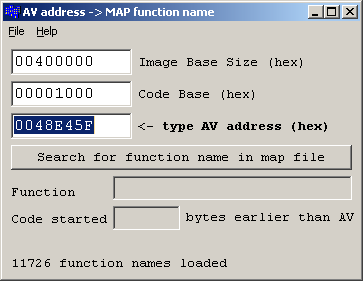
AV to MAP
This small application is searching map file generated by Borland linker (tested with BCB6, BDS2006/Turbo C++ Explorer, Detailed map file type) for name of function that caused Access Violation error. It should be easy to parse map files generated by other linkers too.Address of function in map file can be calculated as:
Map Address <= AV Address - (Image Base + Code Base),
where Image Base is usually 400000h, Code Base is usually 1000h. This application is looking for function address in map file that is equal or greatest smaller than calculated. Keep in mind, that address returned in Access Violation message will be probably useless if error wasn't caused directly by your code but e.g. by WinAPI function called with incorrect arguments (quite often).
AVtoMAP.zip (334 kB with Turbo C++ 2006 sources)
AVtoMAP_test.zip (test application to generate AV with map file, 383 kB)
Much more convenient and reliable would be using some sort of stack trace tool, like JCL Debug, madExcept or EurekaLog.
Skype API communication test/example
This program exchanges messages with Skype using WM_COPYDATA, just like example_win.zip from Skype webpage. Built with BDS2006/Turbo C++ Explorer.executable: skype_test.zip (326 kB)
source code: skype_test_src.zip (47kB), beerware
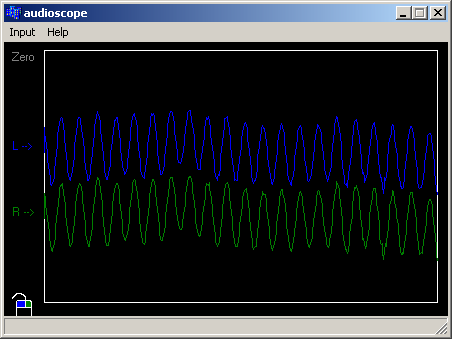
AudioScope
Small application imitating oscilloscope. Using WAVE IN interface.
audioscope.zip (340 kB with sources)
Turbo C++ (BDS2006) project cleaner
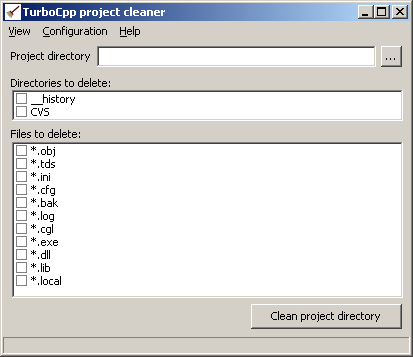
Simple tool that works as not available in BDS2006 "Clean Project" build menu option. Removes
selected types of directories and files (including hidden __history) preparing project dir
to archivization or publication.
Use with caution. Making backup copy of project before cleaning is highly recommended.
turbocpp_clean.7z
Resolution
Tool for fast screen resolution toggling. At first run screen is switched to 800x600 resolution,
at second run to default resolution (if current resolution is same as requested).
Toggled resolution can be changed from command line (shortcut):
resolution resX resY
Code::Blocks project.
resolution.zip
ECC DSA
Test app for easy-ecc,
used as a signature generator in licensing mechanism.
Choosing licensing scheme to small application is not as easy as it seems. Hashes and symmetric cipher
seem are poor choice in a long run as they make it possible to create key generator - tool more acceptable
by end user than crack and usually allowing problem free updates. Asymmetric encryption and signature algorithms
on the other hand is usually quite difficult to integrate as it mostly available as a part of complex and heavy
packages such as OpenSSL or Crypto++ that may substantially increase executable size and in case of any C++ library
difficult to port to compiler that is not on support list (consider C++ compiler without exception support for embedded target).
Easy-ecc library by Kenneth MacKay is definitely a gem, implementing elliptic curve cryptography (these algorithms
are offering very good security to key length ratio) in a form of single C module without any dependencies such as
arbitrary length arithmetic libraries.
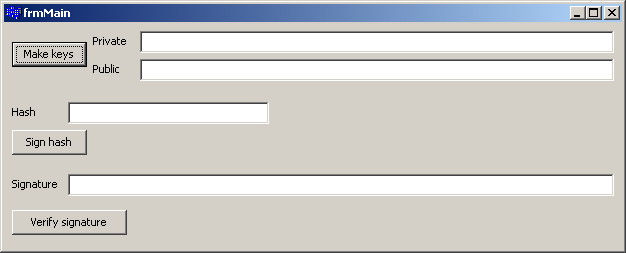
ecc.zip
Low memory warning
Simple, windowless application generating audible warning with PC speaker when memory usage is exceeded.
Use Code::Blocks/MinGW to rebuild and/or change configuration. To terminate use task manager or supplied close.bat file.
memwarning.zip
ObeXplorer
ObeXplorer - file transfer over Bluetooth.
IntelPWMControl
IntelPWMControl - change backlight PWM frequency for LCD panel.
UartTest
UartTest - simple test for UART put in loopback.
JoinMulticast
JoinMulticast - simple application able to join multiple multicast groups for testing purposes.
UdpSender
UdpSender - small app to send binary UDP datagrams.
png2argb
png2argb - small app converting png into Adobe Scripting ARGB hex string.
TOTP generator for github
TotpGenerator.
ICMP ping test
PingTest.
WS2812 test
WS2812 test - controlling WS2812 LED strip from PC UART.
memwarning.zip