tSIP softphone: ZRTP
ZRTP support was added in tSIP 0.2.3.6.
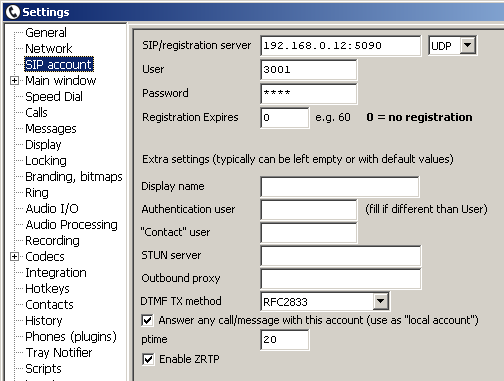
ZRTP can be enabled in account settings:
ZRTP uses Short Authentication String (SAS) that should be compared by call parties to make sure that there is no Man-in-the-Middle attack. In default tSIP configuration SAS is visible only in log, but it can be displayed on designated buttons using script - see Tools/Script/Help/Examples, "Display ZRTP encryption state".
-- "on encryption state" script,
-- displaying ZRTP/SAS state on buttons
local btn1Id = 15 -- set this button configuration to 2 lines
local btn2Id = 16
-- end of settings
local sessionId, zrtpActive, zrtpSas, zrtpCipher, zrtpSasVerified = GetZrtpState()
print(string.format("Lua: ZRTP sessionId = %d, active = %d, SAS = %s, cipher = %s, verified = %d\n",
sessionId, zrtpActive, zrtpSas, zrtpCipher, zrtpSasVerified))
local line1 = "ZRTP not active"
local line2 = ""
local line3 = ""
if zrtpActive == 1 then
line1 = string.format("ZRTP SAS: %s", zrtpSas)
if zrtpSasVerified == 1 then
line2 = "VERIFIED"
SetButtonImage(btn1Id, "lock_green.bmp")
else
line2 = "NOT verified"
SetButtonImage(btn1Id, "lock_yellow.bmp")
end
line3 = zrtpCipher
else
SetButtonImage(btn1Id, "empty.bmp")
end
SetButtonCaption(btn1Id, line1)
SetButtonCaption2(btn1Id, line2)
SetButtonCaption(btn2Id, line3)
This script should be assigned to "on encryption state" scripting event. Choose two buttons for displaying text set by the script - here they are buttons #15 (for SAS and verification state display) and #16 (for cipher name).
Additional bitmaps (lock_yellow.bmp, lock_green.bmp) are used visually signal that ZRTP is active but SAS is not verified and that ZRTP is active with verified SAS.
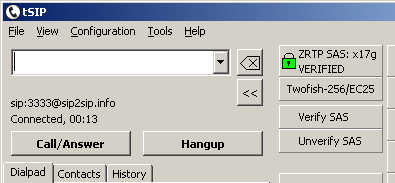
Two additional buttons: "Verify SAS" and "Unverify SAS" are used to store session data to file (zrtp.zid in tSIP directory) allowing to skip verification step on next call with same peer.
Notes:
- button #15 is set to 2-line in this example
- buttons can be freely moved and resized
- buttons in dialpad area are also configurable and used for this purpose, though in default configuration their width might be too small to display whole cipher name
- for button displaying cipher name it might be worth to set caption to horizontally centered
- as buttons used only for displaying purposes have no action in this example, their "Bevel width" might be set to 0 to make them not look like clickable buttons
Back to howto list